The Control Measures That Can Address the Provider's Security Concerns.
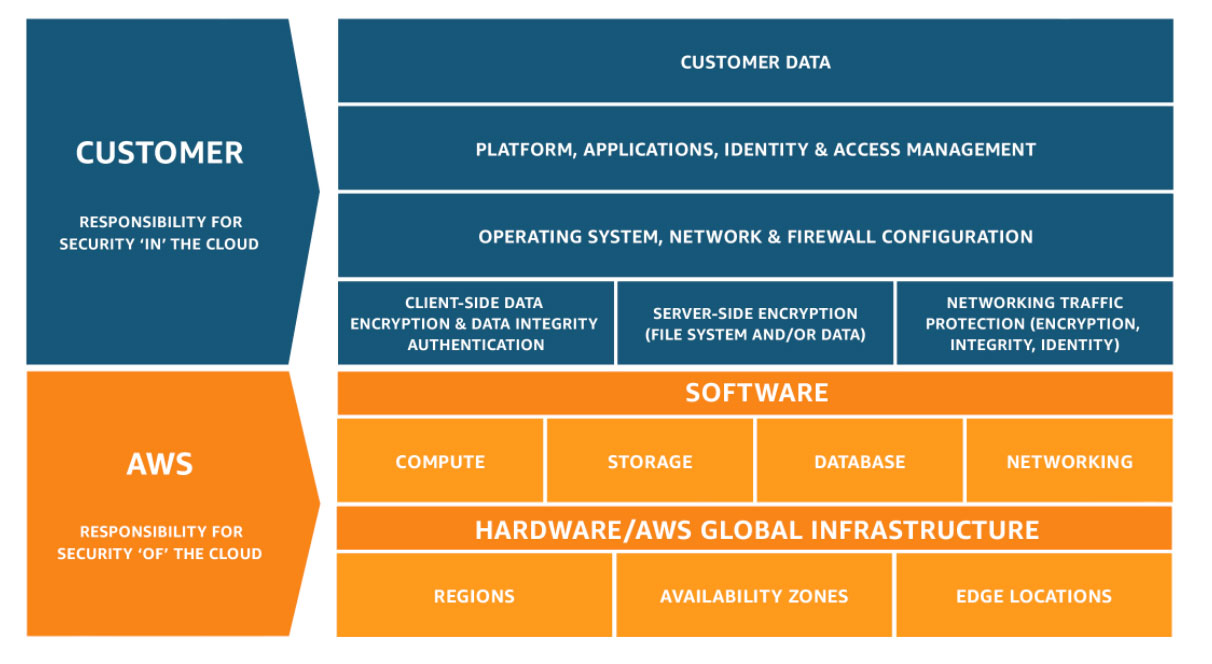
Security and Compliance is a shared responsibility between AWS and the customer. This shared model tin help salvage the customer's operational burden as AWS operates, manages and controls the components from the host operating system and virtualization layer down to the physical security of the facilities in which the service operates. The customer assumes responsibility and management of the invitee operating system (including updates and security patches), other associated application software as well equally the configuration of the AWS provided security group firewall. Customers should carefully consider the services they choose as their responsibilities vary depending on the services used, the integration of those services into their It environment, and applicable laws and regulations. The nature of this shared responsibility also provides the flexibility and client command that permits the deployment. As shown in the nautical chart beneath, this differentiation of responsibility is commonly referred to as Security "of" the Cloud versus Security "in" the Cloud.
AWS responsibility "Security of the Cloud" - AWS is responsible for protecting the infrastructure that runs all of the services offered in the AWS Cloud. This infrastructure is composed of the hardware, software, networking, and facilities that run AWS Deject services.
Customer responsibleness "Security in the Deject" – Client responsibility volition be adamant past the AWS Cloud services that a customer selects. This determines the amount of configuration work the customer must perform as part of their security responsibilities. For example, a service such as Amazon Elastic Compute Cloud (Amazon EC2) is categorized every bit Infrastructure every bit a Service (IaaS) and, as such, requires the customer to perform all of the necessary security configuration and direction tasks. Customers that deploy an Amazon EC2 case are responsible for management of the invitee operating system (including updates and security patches), whatever application software or utilities installed past the customer on the instances, and the configuration of the AWS-provided firewall (called a security group) on each instance. For abstracted services, such every bit Amazon S3 and Amazon DynamoDB, AWS operates the infrastructure layer, the operating organisation, and platforms, and customers admission the endpoints to store and recollect information. Customers are responsible for managing their data (including encryption options), classifying their assets, and using IAM tools to utilize the advisable permissions.
This customer/AWS shared responsibleness model besides extends to IT controls. Just every bit the responsibility to operate the IT surround is shared between AWS and its customers, so is the management, operation and verification of Information technology controls shared. AWS can help salvage customer burden of operating controls by managing those controls associated with the physical infrastructure deployed in the AWS environment that may previously have been managed by the customer. Equally every client is deployed differently in AWS, customers tin take advantage of shifting management of certain IT controls to AWS which results in a (new) distributed control surround. Customers tin then use the AWS control and compliance documentation available to them to perform their command evaluation and verification procedures as required. Below are examples of controls that are managed by AWS, AWS Customers and/or both.
Inherited Controls – Controls which a customer fully inherits from AWS.
- Physical and Environmental controls
Shared Controls – Controls which employ to both the infrastructure layer and customer layers, just in completely split contexts or perspectives. In a shared command, AWS provides the requirements for the infrastructure and the client must provide their own control implementation within their utilise of AWS services. Examples include:
- Patch Management – AWS is responsible for patching and fixing flaws within the infrastructure, but customers are responsible for patching their guest OS and applications.
- Configuration Direction – AWS maintains the configuration of its infrastructure devices, only a customer is responsible for configuring their own guest operating systems, databases, and applications.
- Awareness & Training - AWS trains AWS employees, but a client must train their own employees.
Client Specific – Controls which are solely the responsibleness of the client based on the application they are deploying within AWS services. Examples include:
- Service and Communications Protection or Zone Security which may crave a customer to route or zone data within specific security environments.
Applying the AWS Shared Responsibleness Model in Practise
Once a customer understands the AWS Shared Responsibleness Model and how information technology generally applies to operating in the deject, they must determine how it applies to their use case. Client responsibility varies based on many factors, including the AWS services and Regions they cull, the integration of those services into their IT surroundings, and the laws and regulations applicable to their organization and workload.
The following exercises can aid customers in determining the distribution of responsibleness based on specific apply example:


Review the security functionality and configuration options of individual AWS services inside the security capacity of AWS service documentation.


Provide your internal and external audit teams with deject-specific learning opportunities by leveraging the Cloud Audit Academy training programs.

Perform a Well-Architected Review of your AWS workloads to evaluate the implementation of best practices for security, reliability, and performance.

Explore solutions available in the AWS Market digital catalog with thousands of software listings from independent software vendors that enable you to find, exam, buy, and deploy software that runs on AWS.

Explore AWS Security Competency Partners offer expertise and proven customer success securing every phase of cloud adoption, from initial migration through ongoing day-to-twenty-four hours management.

Have Questions? Connect with an AWS Business Representative
AWS support for Internet Explorer ends on 07/31/2022. Supported browsers are Chrome, Firefox, Edge, and Safari. Learn more »
Source: https://aws.amazon.com/compliance/shared-responsibility-model/
0 Response to "The Control Measures That Can Address the Provider's Security Concerns."
Postar um comentário